Underline | Echo of Neighbors: Privacy Amplification for Personalized Private Federated Learning with Shuffle Model
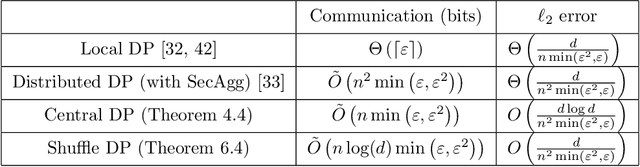
Privacy Amplification via Compression: Achieving the Optimal Privacy-Accuracy-Communication Trade-off in Distributed Mean Estimation: Paper and Code - CatalyzeX

Privacy Amplification with Couplings and Overlapping Mixtures | Rafik Hariri Institute for Computing and Computational Science & Engineering
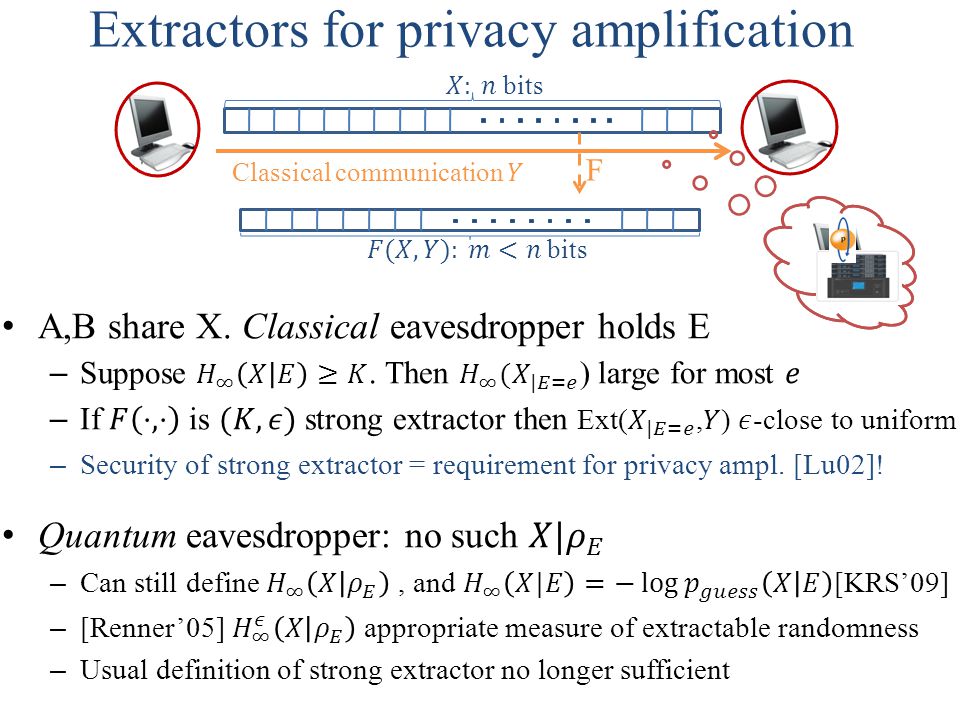
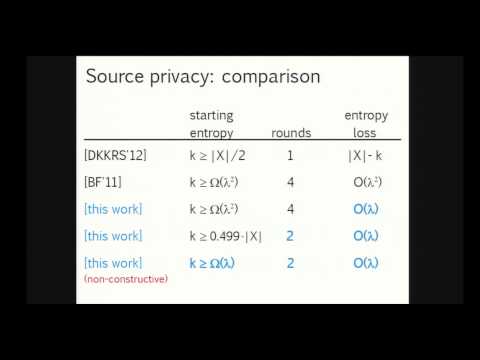
Randomness Extraction and Privacy Amplification with quantum eavesdroppers Thomas Vidick UC Berkeley Based on joint work with Christopher Portmann, Anindya. - ppt download
PPT - Randomness Extraction and Privacy Amplification with quantum eavesdroppers PowerPoint Presentation - ID:4846836
GitHub - rriemann/privacy-amplification: postprocessing for quantum cryptography raw data (master' thesis project)
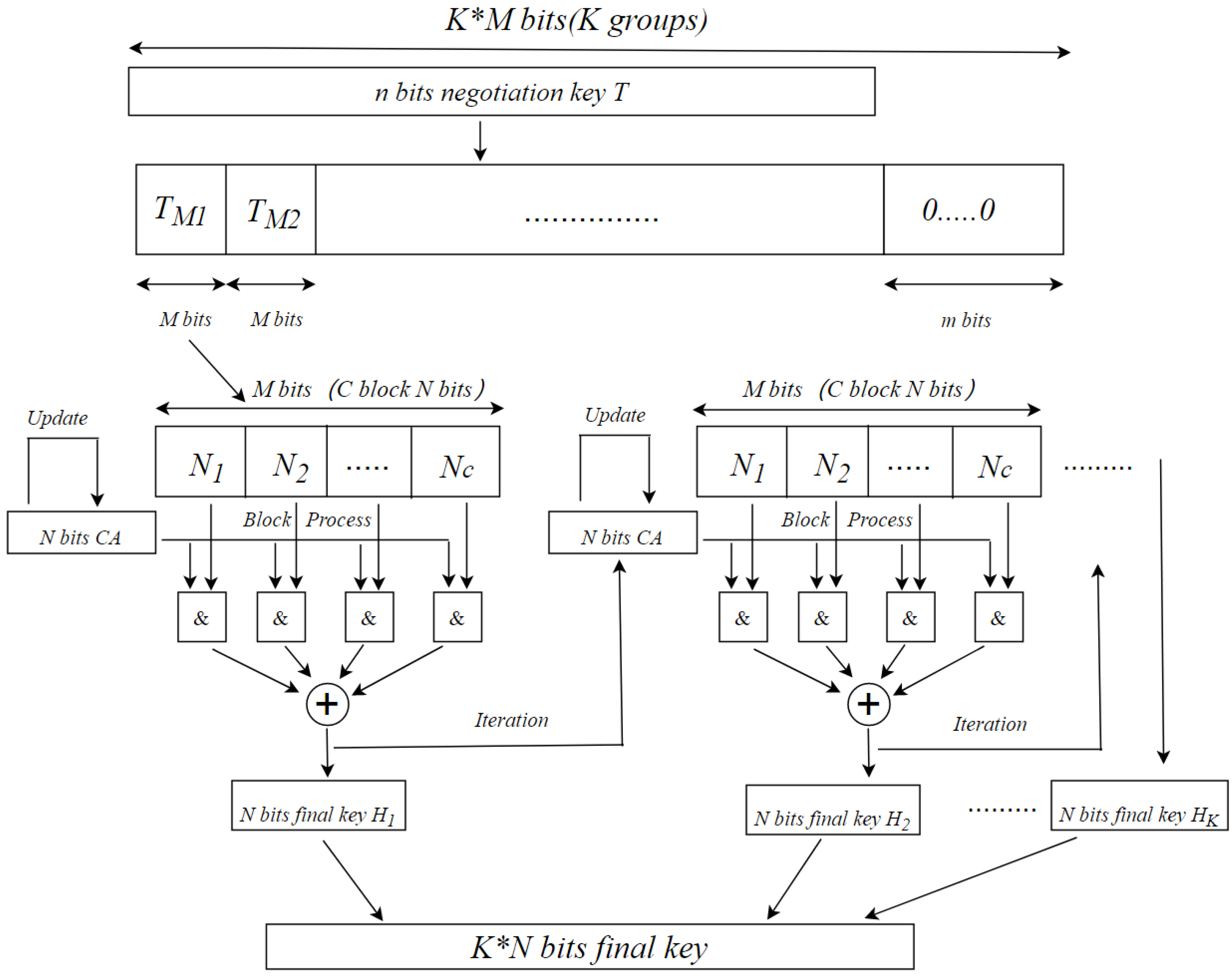
Electronics | Free Full-Text | High-Speed Privacy Amplification Algorithm Using Cellular Automate in Quantum Key Distribution

An efficient hybrid hash based privacy amplification algorithm for quantum key distribution | SpringerLink

PDF) QKD secrecy for privacy amplification matrices with selective individual attacks | Nicola Laurenti - Academia.edu
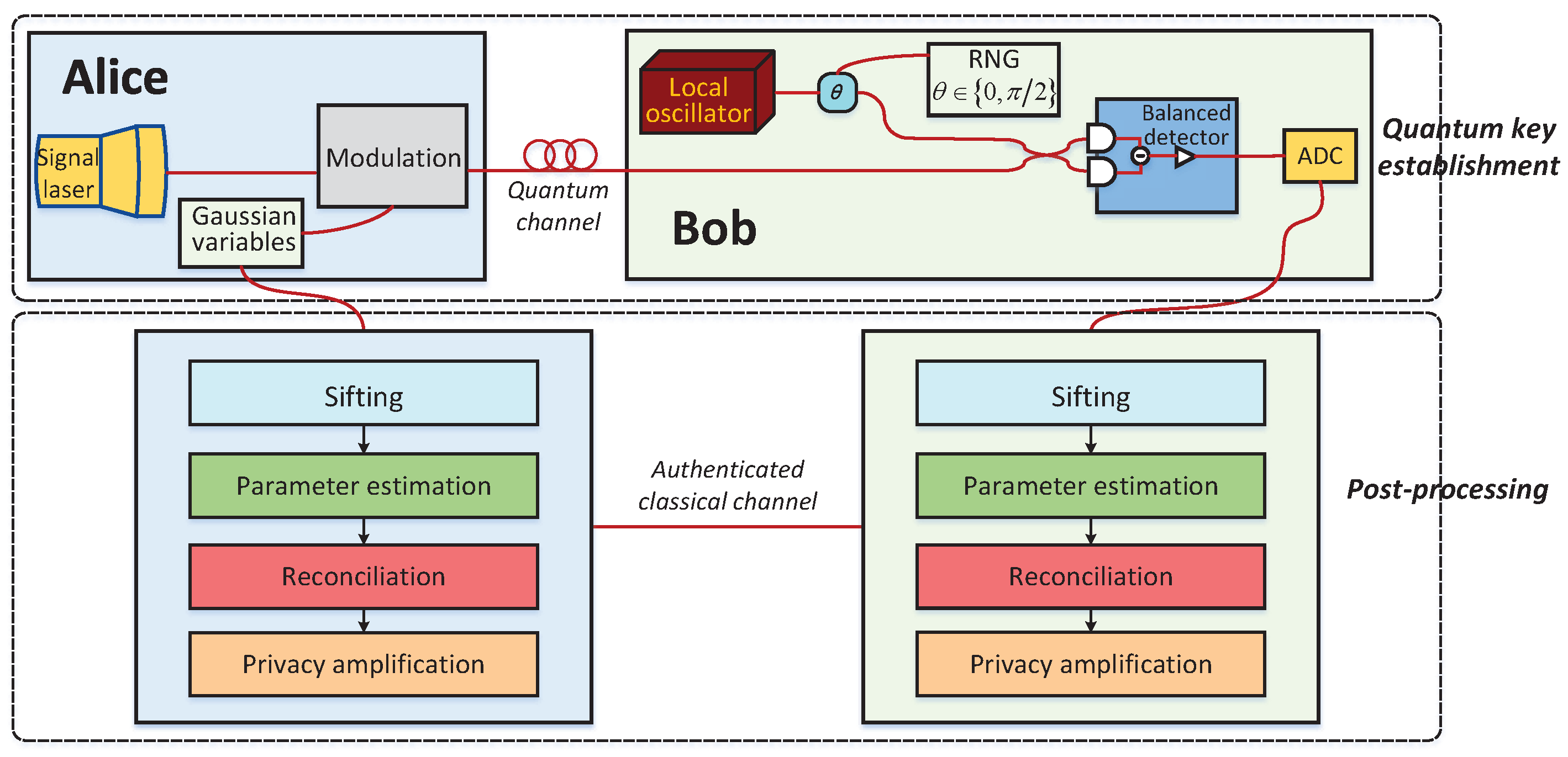
Entropy | Free Full-Text | An Improved Slice Reconciliation Protocol for Continuous-Variable Quantum Key Distribution

High-speed and Large-scale Privacy Amplification Scheme for Quantum Key Distribution | Scientific Reports
Quantum Hash function and its application to privacy amplification in quantum key distribution, pseudo-random number generation and image encryption – topic of research paper in Computer and information sciences. Download scholarly article